Kent Cyber Security Forum 2019
A short write up following the Kent Cyber Security Forum 2019.

I was fortunate enough to have a day out of the office yesterday (5th September 2019) to attend the Kent Cyber Security Forum conference held at the University of Kent. Here's a quick write up of the event.
Keynote #1 - Chris E, NCSC
The National Cyber Security Centre (NCSC), part of GCHQ, is the UK government's body for making "the UK the safest place to live and work online". They've done a lot of good things to help improve the UK's cyber security state, including issuing sensible password guidance and creating the Cyber Essentials scheme to help organisations be more secure.
Our speaker for the first keynote was Chris E. Chris explained the various steps the NCSC had taken and how their approach had changed over the year. For example, in an early meeting with several managers he had a manager walk out at lunch time because "if it's all going to happen anyway, there's no point me trying to do anything". To that end, my take home message from Chris' talk was to not scare people by bombarding them with the doom and gloom that can sometimes be cybersecurity.
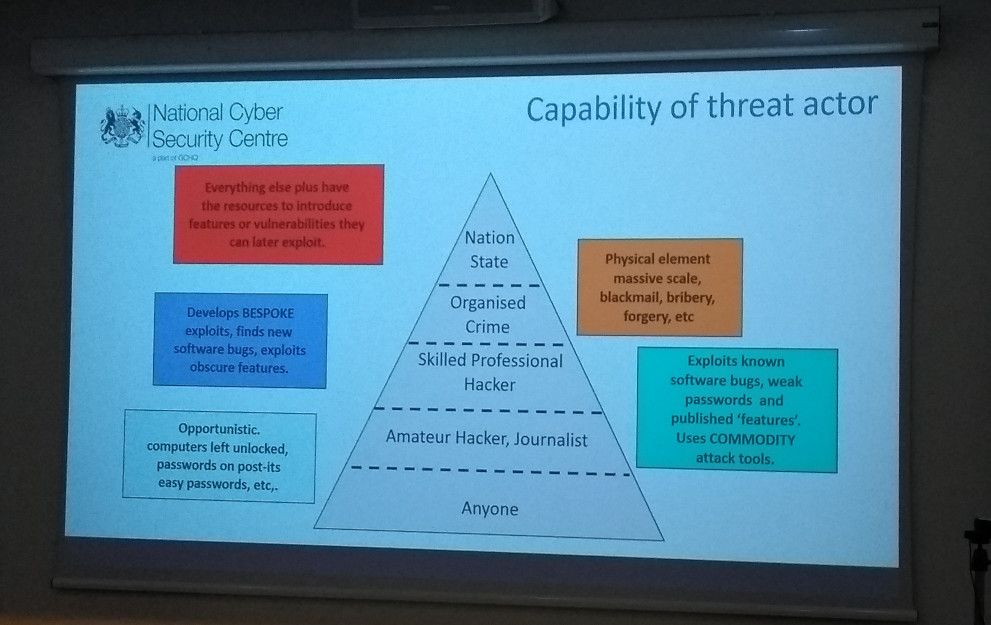
Chris also covered how different threat actors have differing capabilities. Depending on your threat model you'll be protecting against different things. It's the NCSC's hope that through the Cyber Essentials programme no businesses will suffer at the hand of amateur hackers using commodity tools.
Keynote #2 - Dr Jessica Barker, Cygenta
First off, Dr Barker[1] gave the best "who am I?" introduction that I've ever seen. Not just a list of achievements but a bit of insight to her life. Certainly had the audience laughing :) .
Jess' presentation was full of energy and covered how phishing scams (and others) work. Sometimes it's curiosity that hooks the victim, other times temptation or a desire to reciprocate once someone has already been given something. The latter is playing a big part in sextortion scams where the victim may receive revealing pictures from the scammer, then being tricked into returning the favour.
It's often said that "humans are the weakest link in cyber security" and Jess challenged this, calling it a "lazy rhetoric". If humans are the weakest link then we've let that be the case. Training is the solution to this and there's plenty of success stories we don't hear where a human stopped an attack because they knew something wasn't right.
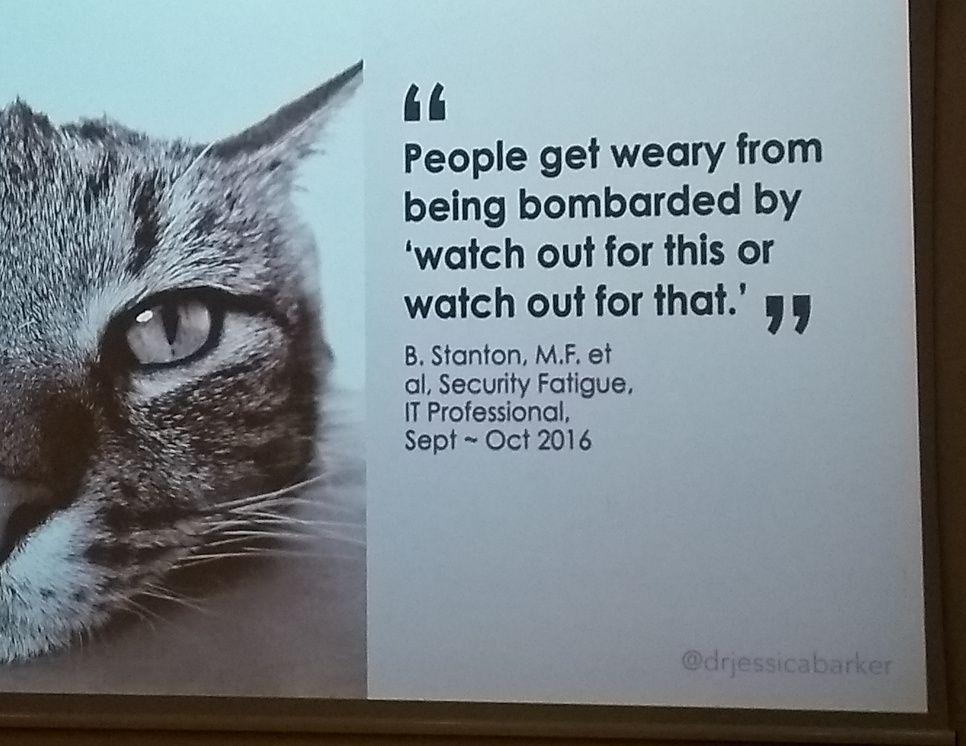
The biggest part of Jess' message, for me, was the move from using negative statistics ("20% of users failed this security test") to positive ones ("80% of staff passed the test, will you join them next time?"). This ties in with Chris E's point from the first keynote about scaring people. The slide above is also quite a key message:
"People get weary from being bombarded by 'watch out for this or watch out for that'. (B. Stanten, M.F. et al, Security Fatigue, IT Professional, Sept-Oct 2016)
My colleague and I agreed there was a need for a change of approach back at the office. Another tip was to set up cyber security champions within the organisation. These sit outside of the security team and provide a (possibly more friendly) point of contact for other colleagues.
Dr Jessica Barker is a co-founder of Cygenta and also a guest on Smashing Security.
Lunch & networking
We were treated to a barbeque with ice cream and various juices and hot drinks. The day was also a good time to network and I met Gareth Corfield from The Register along with catching up with folk I'd met previously. Turns out I know quite a few of the more local people working in this industry (be that lecturing or working in industry).
Keynote #3 - Mikko Hyppönen, F-Secure
Mikko Hyppönen, also a guest on Smashing Security, is F-Secure's Chief Research Officer and he spoke on the cyber arms race. From Mikko's perspective, successful cyber attacks are grouped into people problems and technical problems. The latter likely involves a bug in code, and Mikko reflected that a bug in Microsoft Word used on Windows 3.0 / 3.1 had a very different impact to a similar bug in Microsoft Word on Windows 10. In the early days bugs were inconveniences that crashed your system, perhaps losing your work. As the device wasn't on the Internet (and possibly not a network at all) there was no wider problem.
Not true these days!
Again scam type attacks were looked at as were malware infections. It's important to note not all cyber-criminals are from Russia, "some are from the Ukraine". Mikko's talk probably had the most laughs of the event and he did go on to explain attackers could be from anywhere, not just the aforementioned countries.
There was a particular quote that stuck with me, and I tweeted it during the talk:
"We do not need a notification on our phones to tell us the toast is done."@mikko on putting toasters on the Internet#KCSF2019
— Jonathan Haddock (@joncojonathan) September 5, 2019
The audience was taken through the insanity that is the Internet of Things, as not everything needs to be connected. Moreover, it's not even like we'll be able to block all devices at our gateways - they won't be using our wifi or routers, they'll use 5G or other cellular connectivity. Be wary of purchasing connected devices - does it really need to be online?!
Short talks
The event rounded out with a selection of short talks. Some explained the different schools at the University of Kent while others looked at external organisations or research that had been conducted. Each talk was supposed to be limited to five minutes - some were short, one was on time, but generally they overran. I confess I'm not sure how I'd give an effective talk limited to five minutes, a challenge I may take up at some point.
Conclusion
On the whole this was a good conference and it was nice not to have to travel too far to attend. I'd certainly attend next year if I'm able and I wouldn't mind giving a short talk, albeit probably longer than five minutes!
Banner image is the image used by the conference.
[1] I couldn't decide if it was more appropriate to refer to Dr Barker by title or name, so I've used a mix. I don't know why.

